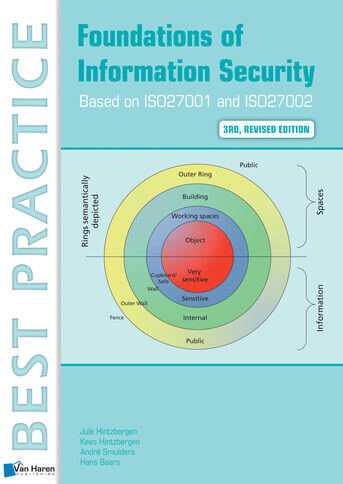
This book is intended for everyone in an organization who wishes to have a basic understanding of information security. Knowledge about information security is important to all employees. It makes no difference if you work in a profit- or non-profit organization because the risks that organizations face are similar for all organizations.
It clearly explains the approaches that most organizations can consider and implement which helps turn Information Security management into an approachable, effective and well-understood tool. It covers:
* The quality requirements an organization may have for information;
* The risks associated with these quality requirements;
* The countermeasures that are necessary to mitigate these risks;
* Ensuring business continuity in the event of a disaster;
* When and whether to report incidents outside the organization.
The information security concepts in this revised edition are based on the ISO/IEC27001:2013 and ISO/IEC27002:2013 standards. But the text also refers to the other relevant international standards for information security.
The text is structured as follows:
* Fundamental Principles of Security and Information security and Risk management.
* Architecture, processes and information, needed for basic understanding of what information security is about.
* Business Assets are discussed.
* Measures that can be taken to protect information assets. (Physical measures, technical measures and finally the organizational measures.)
The primary objective of this book is to achieve awareness by students who want to apply for a basic information security examination. It is a source of information for the lecturer who wants to question information security students about their knowledge. Each chapter ends with a case study. In order to help with the understanding and coherence of each subject, these case studies include questions relating to the areas covered in the relevant chapters. Examples of recent events that illustrate the vulnerability of information are also included.
This book is primarily developed as a study book for anyone who wants to pass the ISFS (Information Security Foundation) exam of EXIN. In an appendix an ISFS model exam is given, with feedback to all multiple choice options, so that it can be used as a training for the 'real' ISFS exam.